Turning Challenges into Solutions
Turning Challenges into Solutions: My Custom Cribl Pack for AWS Security Lake to Sentinel
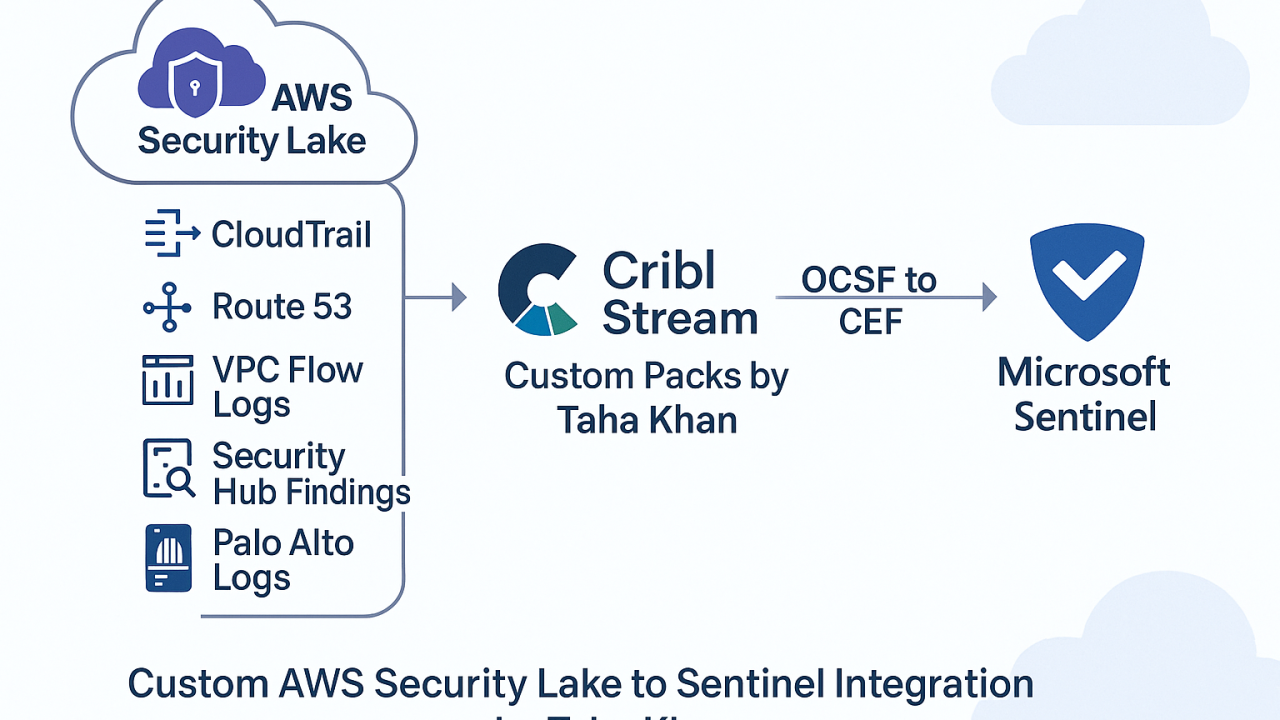
Recently, I was tasked with something that didn’t have a plug-and-play solution—collecting logs from AWS Security Lake and sending them to Microsoft Sentinel using Cribl Stream.
The challenge? ➡️ AWS Security Lake provides data in OCSF (Open Cybersecurity Schema Framework) ➡️ Microsoft Sentinel expects CEF (Common Event Format) ➡️ There was no official Cribl pack available to handle this transformation.
💡 Solution: I developed 5 custom Cribl Packs from scratch to normalize and route logs from:
- ☁️ AWS CloudTrail
- 🌐 AWS Route 53
- 🔁 VPC Flow Logs
- 🔍 AWS Security Hub Findings
- 🔥 Palo Alto Firewall Logs
Each pack transforms the raw OCSF data into Sentinel-friendly CEF format and routes it successfully, ensuring complete log visibility across cloud and security layers. Logs are now flowing seamlessly into Sentinel!
✅ Logs parsed ✅ Fields mapped ✅ Security teams empowered with actionable insights
This was an exciting and technical journey—from researching schemas to building dynamic pipelines with Regex, Eval, Serialize, and more in Cribl.
🔧 Tech Stack: AWS Security Lake | Cribl Stream | Microsoft Sentinel | OCSF → CEF normalization
👨💻 If anyone is working on something similar and looking to bridge OCSF-to-CEF in Cribl, I’d be happy to connect or help!
